Texas app store age verification law blocked by federal judge

A Texas federal judge today blocked an App Store age verification law that was set to go into effect on January 1, 2026, which means Apple may not have to support the changes after all. The Texas App Store Accountability Act (SB2420) requires Apple and other app marketplaces to confirm user age when a person […]
X-ray: a Python library for finding bad redactions in PDF documents
x-ray is a Python library for finding bad redactions in PDF documents. At Free Law Project, we collect millions of PDFs. An ongoing problem is that people fail to properly redact things. Instead of doing it the right way, they just draw a black rectangle or a black highlight on top of black text and […]
Some Epstein file redactions are being undone with hacks
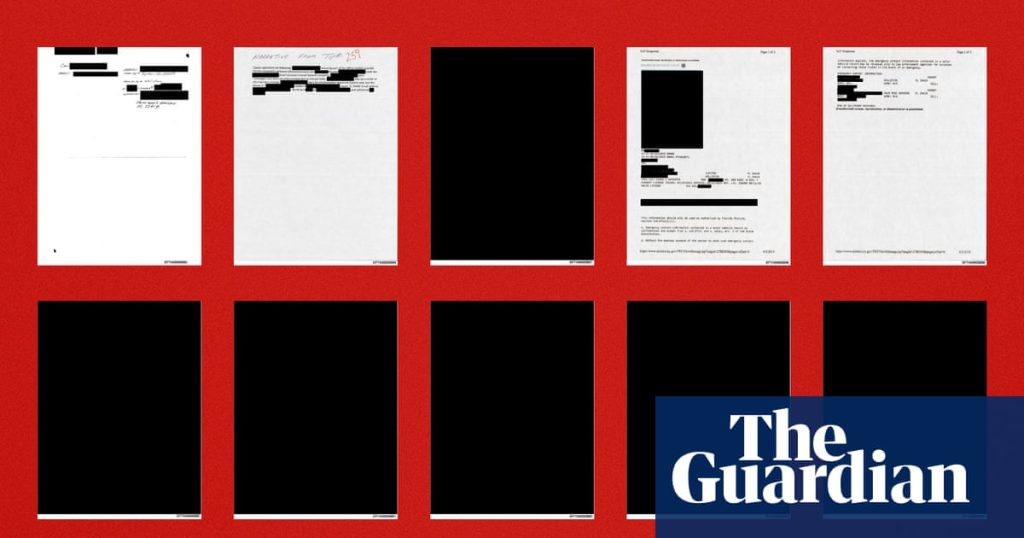
People examining documents released by the Department of Justice in the Jeffrey Epstein case discovered that some of the file redaction can be undone with Photoshop techniques, or by simply highlighting text to paste into a word processing file. Un-redacted text from these documents began circulating through social media on Monday evening. An exhibit in […]
HTTP Caching, a Refresher
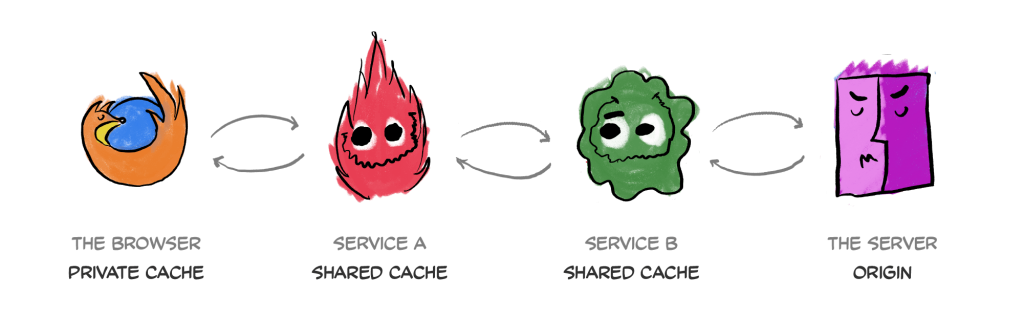
Published Dec 22, 2025 This is a reading of RFC 9111 (2022), the latest iteration of the HTTP Caching standard. It defines the Cache-Control HTTP header as a way to prescribe how caches should store and reuse HTTP responses, with regards to not just the browser cache, but to any other intermediary caches, such as […]
Terrence Malick’s Disciples
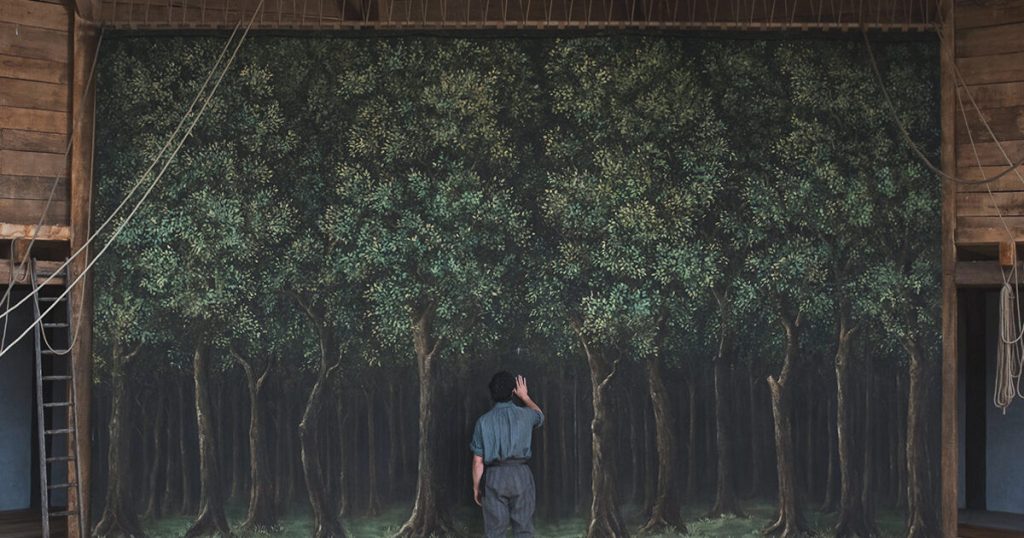
Why the auteur is the most influential director in Hollywood Paul Mescal in Hamnet, directed by Chloé Zhao, 2025. Photo by Bruno Engler, courtesy Paramount Pictures In the winter of 2024, the photographer and filmmaker RaMell Ross released Nickel Boys, a masterful adaptation of a novel by Colson Whitehead. In a fragmentary, impressionistic style, the […]
Un-Redactor

A PDF editing tool that lets you put your own information over a redaction box. This tool is for forensics purposes. It does not “recover” data truly destroyed by redaction tools. What it does do is allow you to write over a redaction box. Like white-out. You can select a redaction box, and select all […]
Help My c64 caught on fire

I flew back to Italy for the Christmas holidays, as I usually do. Here I have my childhood c64, on which I learend how to program, and which in the last few years I took to refurbishing.In general, everytime I’m back to my parent’s place I spend some time fixing and sorting out things, and […]
2025 was the year Xbox died

Want to see a dead body? I present to you the Xbox. After a subdued launch at the height of the COVID pandemic in 2020, the Xbox Series X quickly lost the fight against the PlayStation 5. Microsoft simply couldn’t deliver enough compelling games, despite some huge acquisitions, while Sony leaned on its goodwill from […]
Clock Synchronization Is a Nightmare
Time seems simple. But we engineers lose sleep over something as basic as keeping clocks in sync. Here’s why… The answer lies in this one simple statement – there is no global clock. When you have thousands of machines spread across data centers, continents, and time zones, each operating independently, the simple question of “what […]
Volvo Centum is Dalton Maag’s new typeface for Volvo

Volvo will celebrate its centennial in 2027 and the company is already starting to ramp up the celebrations. Last year saw the opening of the World of Volvo in Gothenburg, a vast circular timber structure designed by Scandinavian design specialists Henning Larsen. Volvo Centum typeface by Dalton Maag (Image credit: Volvo) 2026 will see another […]